KakaoTalk数据库密钥
KakaoTalk的数据库为sqlite3数据库,经过加密处理,不同类别的数据库采用不同的密钥加密。聊天记录的数据库由一个称为PRAGMA KEY的密钥进行加密,这里简称为PK。
PK的生成
PK的格式如下:
ODSnnkkwyAHsXwgCEIQLCpAxdSZhGsKegV0Y8EsSd74dV5szZ37+CsqNKGkxIlZfg8p5VXIPd/LTjoRj2kFx4A==410545402
由2部分组成,即一个Hash的Base64编码值 + 登录成功后服务器返回的唯一标识,这里简称这个唯一标识为UID。
基本算法如下
PK_Hash = SHA512(AES-128-CBC(UUID + Disk Model Name + Disk SerialNumber))
PK = Base64Encode(PK_HASH) + UID
首先获取主机系统的UUID,通过命令行获取方式如下:
wmic csproduct get "UUID"
也可通过编码方式获取
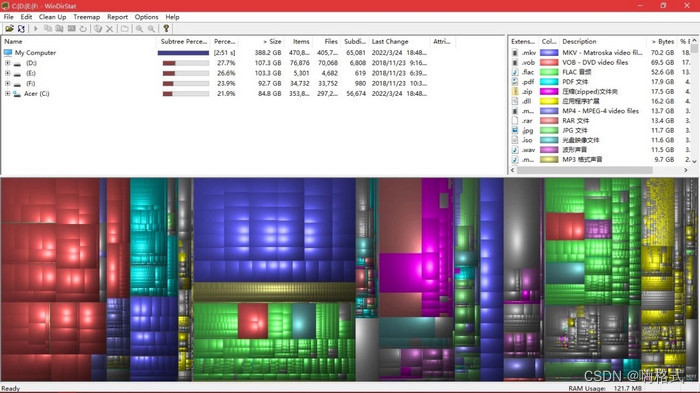
然后获取主机系统所在磁盘名Model、磁盘序列号SerialNumber,通过命令行获取方式如下:
wmic diskdrive get Model, SerialNumber
将以上获取的元素信息拼成字符串
4D5882F5-E72C-41E0-9ADA-E2DAD13438C6|Samsung SSD 870 EVO 1TB SCSI Disk Device|S6PVNX0A101380D
因为后面要进行AES-128-CBC加密,所以需要Padding,按16字节对齐后
4D5882F5-E72C-41E0-9ADA-E2DAD13438C6|Samsung SSD 870 EVO 1TB SCSI Disk Device|S6PVNX0W101380D\x03\x03\x03
或如
D1EA91EE-8E1C-D4C3-D204-0C9D9280E10B|Samsung SSD 860 EVO 250GB|S4CKNF0NB09400F\x02\x02
AES-128-CBC key的生成
SHA1(BIN(1DC1B6C365BA5451DA4F730F237CF6635E272D273636363636363636363636363636363636363636363636363636363636363636363636363636363636363636)) = 9FBAE3118FDE5DEAEB8279D08F1D4C79
其中
BIN(1DC1B6C365BA5451DA4F730F237CF6635E272D273636363636363636363636363636363636363636363636363636363636363636363636363636363636363636)是KakaoTalk内置固定值,所以最终的SHA1值9FBAE3118FDE5DEAEB8279D08F1D4C79也是固定值。
最终AES-128-CBC密钥组成如下:
key: 9FBAE3118FDE5DEAEB8279D08F1D4C79
iv: 00000000000000000000000000000000
使用AES-128-CBC加密拼接后的字符串
AES-128-CBC("4D5882F5-E72C-41E0-9ADA-E2DAD13438C6|Samsung SSD 870 EVO 1TB SCSI Disk Device|S6PVNX0W101380D\x03\x03\x03") = E68133E9 ... D397E363752
使用SHA512计算加密后的HASH值
SHA512(BIN("E68133E9 ... 7E363752")) = 3834a79e ... da4171e0
使用Base64进行编码
Base64Encode(BIN(3834a79e ... da4171e0)) = ODSnnkkwyAHsXwgCEIQLCpAxdSZhGsKegV0Y8EsSd74dV5szZ37+CsqNKGkxIlZfg8p5VXIPd/LTjoRj2kFx4A==
最后就是获取用户唯一标识UID,该UID在登录成功后由KakaoTalk服务器返回,所以可以通过抓包的方式提取;通过分析,发现KakaoTalk的进程虚拟内存中也存在UID,主要为残留在的内存中的HTTP数据库格式中,可以通过WinHex搜索KakaoTalk进程内存获取UID。
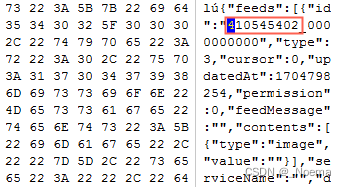
来自服务器的用户UID: 410545402
最后得到PK值
ODSnnkkwyAHsXwgCEIQLCpAxdSZhGsKegV0Y8EsSd74dV5szZ37+CsqNKGkxIlZfg8p5VXIPd/LTjoRj2kFx4A==410545402
数据库密钥的生成
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\chatLogs_***.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\chatListInfo.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\openLinkListInfo.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\talkfile.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\talkmedia.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\TalkUserDB.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\floatingList.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\CalendarDB.edb
以上数据库密钥生成方法:
用PK循环拼接,凑够512字节,大于512字节截取512字节,然后计算512字节的MD5值最为key值,
key = MD5(PK * 512)
iv = MD5(Base64Encode(BIN(key)))
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\talk_user_prf.edb
以上数据库密钥生成方法:
pk_b64 = Base64Encode(BIN(MD5(PK)))
key = MD5(pk_b64 * 512)
iv = MD5(Base64Encode(BIN(key)))
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\Contacts*.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\url_image_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\ocii_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\oci_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\mci_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\gfve_t_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\gfbe_t_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\fci_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\chat_data\cli_http_v2.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\OCH*.edb
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\DigitalItem*.edb
以上数据库密钥生成方法:
pk_sha512 = SHA512(PK)
key = MD5(pk_sha512 * 512)
iv = MD5(Base64Encode(BIN(key)))
KakaoTalk\CardList*.edb
KakaoTalk\OpenLinkPreset*.edb
以上数据库密钥生成方法:
pk_hash_sha512 = SHA512(PK_HASH)
key = MD5(pk_hash_sha512 * 512)
iv = MD5(Base64Encode(BIN(key)))
这里计算的是PK_HASH的SHA512不是PK
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\MultiProfileDB.edb
以上数据库密钥生成方法:
key = MD5((multiprofile + PK) * 512)
iv = MD5(Base64Encode(BIN(key)))
KakaoTalk\users\5fea7626aa67c9a1771a5187f2d76a0f72cea0ba\emoticon.edb
以上数据库密钥生成方法:
pk_b64 = Base64Encode(BIN(MD5(emoticon + PK_HASH + emoticon)))
key = MD5(pk_b64 * 512)
iv = MD5(Base64Encode(BIN(key)))
聊天缓存文件密钥生成方法(该密钥可以解密缓存文件)(解密算法AES-128-CBC)
key = MD5(PK)
iv = MD5(Base64Encode(key))
资源文件(.xml)key、iv计算:
key = MD5("KAKAOTALK_PC_FOREVER")
iv = MD5(Base64Encode(key))
这里的KAKAOTALK_PC_FOREVER为KakaoTalk内置固定字符串。
connect_conf文件内容解密:
密钥生成方法:
key = MD5(PK_HASH + 20150201)
iv = MD5(Base64Encode(key))
mss.dat文件内容解密:
密钥生成方法:
key = MD5("PK_HASH20220725")
iv = MD5(Base64Encode(key))








![[VNCTF2024]-PWN:preinit解析(逆向花指令,绕过strcmp,函数修改,机器码)](https://img-blog.csdnimg.cn/direct/a25d17ccb3bd424f8e88d47e6ea67e8d.png)